| Previous
Page |
PCLinuxOS
Magazine |
PCLinuxOS |
Article List |
Disclaimer |
Next Page |
Is There A VPN In Your Future? |
|
by Paul Arnote (parnote) Ok. I know how some get their britches twisted into knots when something I write is perceived to have "political" overtones. So, this I'm about to say is definitely NOT about politics. Rather, this is about what this all means, not only to U.S. users, but those who also communicate with U.S. users, and the ramifications and fallout that's expected. Like it or not, sometimes the things that happen in the political arena have an effect on the daily lives of folks who would rather remain apolitical. Back in 2013, the U.S. government passed a set of "net neutrality" laws. Among the restrictions it put into place, ISPs were not allowed to mine the data and online habits of their users without users "opting in." The broadband industry vehemently opposed these restrictions, since they had their eyes and hearts (and wallets) set on selling user data about what users searched for online, who they emailed, what they did online, etc. to whomever was willing to pay for that data. Very recently (around the end of March, 2017), the U.S. legislative branches capitulated to the will of the broadband industry, forsaking the privacy of the users, and repealed that restriction, which was to take effect December, 2017. What this means for the average user is that all of their internet searches, who they email, and all of their other online activity is available to anyone willing to pay for it.  It's official. You have NO online privacy. By repealing the FCC (Federal Communication Commission) rule, you don't even have an expectation that anything you do online will remain private. All of your online activity is up for sale to the highest bidder. Did you get into a spirited conversation with another individual? Did you search for ________? Did you say something in jest that, taken out of context, could be taken in a different manner than you (and your conversation partner) understood it to mean at the time? The potential ramifications are HUGE. Even the EFF has come out in strong opposition to the repeal of the rule. The fallout remains to be seen. It isn't a huge leap to expect that those who value their privacy will soon be finding a good VPN (Virtual Private Network) to help protect that very same privacy. I can only imagine that those who run VPN services must be jumping up and down with joy over the recent repeal of the rule. They are certain to see an explosion of new subscribers. But what about the average, less-than-tech-savvy user who doesn't know about using a VPN to enhance their online privacy? These poor, unsuspecting souls are like meat about to be run through a grinder. Like I mentioned before, this isn't meant to be a political commentary or anything of the sorts. Rather, those of us who value our privacy must be made aware of these types of things so that we can take the necessary steps to protect our privacy. Knowledge is, after all, power. If you lack the knowledge about the rule change, then you will also lack the power to tip things back in the favor of your privacy. Since all of this has happened, interest in the U.S. has skyrocketed in VPNs. So, what does a VPN offer you that helps protect your privacy? NOITPYRCNE  Just in case you didn't catch that, the subheading is "encryption" spelled backwards. With the use of a VPN, you connect to the internet through your local ISP. However, you local ISP has absolutely NO idea what you are sending from your computer or receiving to your computer when you use a VPN. That's because both ends of the VPN connection are encrypted. The data you send is encrypted before it leaves your computer, and decrypted at the VPN server. Likewise, the data that is sent from the VPN server is encrypted prior to being sent to your computer, where it is decrypted once it arrives. All that your ISP sees is traffic, without the ability to tell what kind of traffic you are sending and receiving. Thus, your ISP has no idea if that traffic is an internet search, torrents, online chat, video streaming, file sharing, or anything else. Because they cannot see what you are doing, they cannot mine your data. And if they cannot collect data on what you are doing, what you are searching for, etc., they cannot profit from selling that data to advertisers. Of course, the encrypted traffic between your computer and your VPN also protects your privacy from the prying eyes of those three and four letter government agencies. Most of the traffic between your computer and your VPN is encrypted -- minimally -- with AES 256 encryption. Lots to choose from You have a LOT of choices out there when searching for a VPN provider. In fact, you can quickly become overwhelmed by all the choices out there. There are free VPN providers, and there are VPN providers you have to pay a monthly or annual subscription fee. But this is just the beginning of the things you need to consider when making your choice of a VPN service. Besides budgetary limitations and considerations, there are other things to consider. First, and probably foremost, is whether or not the VPN service keeps logs. These logs can be used to identify what you are doing while connected to the VPN service. The PCLinuxOS Magazine once ran an article (September 2013) about a free VPN service called VPNBook. They claimed to not keep or maintain logs of their users' VPN sessions. But, that wasn't entirely true. Repeatedly, logs (that they said they didn't keep) kept being entered into evidence in court trials against Anonymous members. In that same issue, we ran another article extolling the (mis)deeds of VPNBook, and offered up alternatives that PCLinuxOS users might want to consider using as a replacement, as well as reasons then why you might want to consider the use of a VPN service. All of those reasons listed in the 2013 article are still just as valid today as when they were written nearly four years ago.  Which brings us to another thing you will need to consider: how much do you trust your new VPN provider? Some VPN providers haven't been around long enough to garner a reputation one way or another, positive or negative. In those cases, you're pretty much operating on blind faith. Others have been around for long enough, with enough users, to have solid reputations, both positive and negative. Like with VPNBook, they could tell you one thing -- like them not keeping logs of your online activity -- but then do something entirely opposite. For what it's worth, VPNBook is still operating a VPN service. I am unaware if they have changed their business practices. Most consumers won't go back to a service once they've been burned, or know of a provider's penchant for dishonesty. While you're encrypting the traffic between your computer and your VPN service, who's to say that your VPN provider isn't collecting and selling your information on the other end, just as your ISP might do if you weren't using a VPN? Typically, VPN services won't, because they won't be in business for long if they did. Word would get around pretty quickly. But who's to say that there aren't a few unscrupulous operators out there to make their quick buck and then disappear into the night? Most who provide a VPN service fully understand their role and their market niche, which should keep their performance in line with the expectations of their customers. Another thing to consider is that you may end up subjecting yourself to the laws of another country (regarding copyright, what's acceptable use and what's unacceptable use, etc.), based on what country the company that operates the VPN service is "based," or where their servers are based. It's not always quickly apparent which applies. One service (which I'll talk about later) has its domain registered in Sweden, its business registered in Malta, and at least one of its servers located in France. Make a GOOD choice With so many choices around for VPN service providers, it might be difficult to figure out which one is right for you. Fortunately, one guy has made it his "mission" to help users like you and me at least make an informed and educated decision about VPN service providers. That One Privacy Site, run by "That One Privacy Guy," features a selection of charts that compare VPN service providers. You can choose from a simple comparison chart, or from a detailed comparison chart. The entire chart may be a bit difficult to view online. To make it easier to study, he has provided the various charts in both Excel *.xlsx and OpenOffice/LibreOffice *.ods Calc files that you can download and compare offline. Select which version of the chart you want to download -- simple or detailed -- and you will be presented with a link to download the appropriate file. You might have to scroll down a bit to see the links. With that said, Lifehacker has recently been featuring quite a few articles on VPNs lately ... well, ever since the rule change was voted on by U.S. legislators. They ran an article on what they viewed to be the five best VPN providers, and even asked their readers which VPN provider was their favorite. The "winner" of the reader poll on Lifehacker was Private Internet Access, a.k.a. PIA. Indeed, they sound like the role model of VPN providers. They have expanded their customer base by providing a honest service with integrity. They do not keep logs of your activity, and are very affordable. You can pay monthly ($7 U.S.), or you can pay yearly ($40). By far, the yearly rate is the best deal, coming in at $3.33 (U.S.) per month. From the Lifehacker article:
PIA is one of those VPN service providers that both protects your privacy and security by encrypting all of the traffic between your home computer (or home network) and their service, but also anonymizes it and helps you get around regional content restrictions by giving you a choice of exit servers (close to 1000, in 10 different countries.) PIA doesn't log data about your session or connection details, they don't discriminate against protocols or IP addresses, and they don't host any data about its users activities at all. They support a number of different authentication and encryption methods, support virtually every mobile and desktop operating system, and their pricing isn't bad either ($7/mo or $40/yr for up to five devices connected simultaneously.)
I did download the installer from PIA, and paid for a one year subscription. So, if you decide to go with PIA, there are a few things you will need to do to get the installer to work on PCLinuxOS. First, you will need to install sudo from the PCLinuxOS repository. Keep in mind that PCLinuxOS is one of the few Linux distros around that shuns the routine use of sudo, opting instead for the much more secure su method of elevating user privileges. Next, you will need to edit the /etc/sudoers file. Right after line 72 of the sudoers file, you will need to add a line that reads something like this: parnote-toshiba ALL=(ALL) ALL Of course, you will replace "parnote-toshiba" with the name of the user you want to allow elevation of user privileges. While you're editing the sudoers file, remove the "#" from in front of line 82. Above all, DO NOT edit the /etc/sudoers file with anything but a simple text editor. On my computer running Xfce, the simple text editor is Mousepad. On LXDE it would be Leafpad. On KDE, it would be KWrite or Kate. On Mate, it would be Pluma. Other good choices would be Geany, Vim, Emacs, Nano, Pico, Gedit, gVim, or (the tool designed for the job of editing the sudoers file) visudo. However, if you aren't familiar with how to navigate in vi (or use its relatively obscure commands), visudo might not be the best choice for you. LibreOffice, AbiWord or any other word processor SHOULD NOT BE USED. There is a huge difference between a simple text editor and a word processor, and a file edited and saved with a word processor very well might just leave you with a corrupted sudoers file. Next, add the user to whom you want to grant sudo privileges to the sudo group in the PCLinuxOS Control Center. Launch the PCLinuxOS Control Center, go to System, and select "Manage users on system." If the group sudo does not exist, add it. Then, double click on the username you want to have sudo access, and make sure that user is a member of the sudo group. Now, go to the directory where you saved the installer files to, and open a terminal session. As a regular user (as in, not root), enter ./pia-v68-installer-linux.sh. Later versions of the Linux installer will require you to change this line to match the name of the installer file (this is the current name of the installer file as of the writing of this article). If you've installed sudo and properly edited your sudoers file, everything should install just fine. 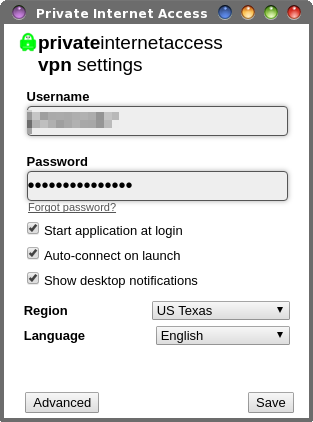 Remember that the admonition about installing from outside the PCLinuxOS repository still stands. Once installed, you should see a red padlock icon in your notification area, and you should be presented with the PIA Settings window (above). On your first run of the settings window, you will need to enter your password. I also checked all of the options in the lower half of the window. To connect to the PIA VPN, right click on the red icon in your notification area and select either "Connect Auto" or the location of the server you want to connect to. While it's connecting, the icon will change from red to gray, and then turn green when your connection has been established. Since I have selected it in the PIA Settings window, my VPN connection is set to start at login, and to auto-connect on launch. PIA will remember the last server you connected to, and reconnect you to it the next time you connect. You can always select a different server from the list at any time you choose. Currently, PIA is running over 3100 servers in 25 different countries. Admittedly, it took me a few times to install it properly. My issue had to do with not having to deal with sudo and the sudoers file since my very brief time with Ubuntu 10 years ago. During that time, I probably forgot more about sudo than I ever knew. Back then I was also a Linux noob, and really didn't yet have a grasp of everything that was going on.  If a free VPN service is more your speed (or all you can afford), there is a newer service available that seems to be on the up and up. Remember that service I mentioned earlier who had registered their domain in Sweden, registered their business in Malta, and had at least one server in France? Well, that VPN provider would be freevpn.se. These guys seem to be too new to even appear on "That One Privacy Guy's" list of VPN providers. I have tried them, with very good results. In fact, I'm writing this article in Google Docs while connected through their VPN service. Earlier in the day, I streamed a torrent video with excellent results. Despite the really good performance, I consider the "jury to still be out" on these guys. One question I keep asking myself is how do these guys afford server space/time by giving it away for free? Color me jaded, but in today's profit driven, greedy world, I just don't see people, much less companies, doing something out of the goodness of their heart. They HAVE to have an income source to stay in business. Nice rhetoric and good intentions don't go far towards paying the bills that will inevitably accompany any endeavor. You connect to freevpn.se through openvpn (in the PCLinuxOS repository). Just download their certificate file(s), and extract them from the archive. On my computer, I've placed those files in their own directory in a directory I created in my /home directory, called VPN. I start the VPN with this command (all on one line), from a root command line:
From what I can tell, most of the VPN service providers support openvpn, which is pretty much a standard on Linux. So whichever method you choose to connect to your VPN service provider, you should be covered and have a fairly painless experience. Summary If you value your privacy, you are going to have to take matters into your own hands. Your politicians don't seem to be too motivated to protect it (but watch them squawk like a wounded chicken when theirs is violated). There is another option, and that is to use the Tor browser and network. Anonymity and privacy are its cornerstones. But that is another story for another time. At this time, VPN service providers are getting most of the attention, and rightly so. The Tor browser and network have a reputation for being slow, even on broadband connections. VPNs work right now, with the programs you're already using. I started with using freevpn.se, before forking over the cost for the paid PIA VPN service. While both seemed to work well, using PIA was a much easier experience. PIA's reputation also went a long way towards putting to rest any doubts I might have had about the integrity of the VPN service. Both appear to be a good choice, at least until they (or someone) proves them to be untrustworthy, like VPNBook. If you can afford the modest cost, I'd recommend you go with a paid VPN service provider, like PIA. |