| Previous
Page |
PCLinuxOS
Magazine |
PCLinuxOS |
Article List |
Disclaimer |
Next Page |
Short Topix: Kernel Lockdown Feature Coming To Linux |
|
by Paul Arnote (parnote) Password Psychology Analyzed  You've heard it all before. Don't reuse passwords from site to site. Use a unique password for each site you visit. However, it seems unlikely, despite ALL of the security breaches that we constantly hear about in the news, that this unsecure habit is about to change anytime soon. Day after day, pilfered user credentials go up for sale on the "Dark Web." LastPass (makers of the popular web browser password manager) and Lab42 partnered up to survey adults around the world to see if they could figure out why, after all the information out there about the risks of password reuse, users continue the risky behavior. The nuts and bolts of the survey was released as an infographic on the LastPass blog. The meat of the survey results is in an executive report (PDF) from LastPass and Lab42. If you're the least bit concerned about online security, both the infographic and the executive report are good and fairly interesting reads. Here at The PCLinuxOS Magazine, we've covered password security several times, including strategies for how to create unique, secure passwords. Remember that your online credentials are a form of currency, especially among the less-than-scrupulous hackers and users of the "Dark Web." Using a secure and unique password for each site you visit that you must log onto means that ONLY that particular password for that particular website is compromised in the event of a data breach. All of your other passwords for other websites remain secure, protecting your private online data. Why Chrome Gobbles So Much RAM & How To Tame Its Appetite  If you read my articles frequently, you know that I really don't care much for the Google Chrome web browser. Yes, I know it's the most popular web browser in the world at this time, but I abhor its voracious appetite for RAM and CPU cycles. Unless you have an abundance of RAM and a very fast CPU, using it can be slow and cumbersome. Well, the reason Chrome consumes so much RAM and so many CPU cycles is because each tab -- and in some instances certain page elements -- are loaded into separate processes, each consuming those precious computer resources. It stands to reason that the more tabs you have open at any given time, the more RAM and CPU cycles Chrome is going to consume. The reason for this is so that if one tab or page element crashes, the other tabs or page elements are (hopefully) not affected. Then, Google Chrome pre-renders the pages, in an effort to enhance your web experience. THEN, you can add in poorly written browser extensions and web pages that might, over time, leak memory. The next thing you know, all of your available RAM is consumed, and your CPU is chugging along at 80%+ usage. We won't even talk about how Chrome phones home to Google with ALL of your browser activity. Fortunately, you can quickly figure out the culprit of who's being the major memory and CPU cycle hog. Press Shift + Esc to display Chrome's internal task manager. Look to see which tabs and/or extensions are consuming the most memory. If it's a tab, you will know which one(s) to close. If it's an extension, you will know which one you will need to uninstall. Despite its features, it might not be worth the memory and CPU cycle drain. According to an article on Lifehacker, there are also some extensions that will help lighten the memory and CPU load for Chrome. The Great Suspender will suspend tabs after a certain amount of time of inactivity. The tabs will remain open, but will take a little extra time to display when you switch to them if they have been put into a suspended state. OneTab takes a different approach. When you have a bunch of tabs opened up, hit the OneTab button. All the tabs will be closed, and a single tab will open in their place, with the URL of each of the previously opened tabs listed. You then click on the link to open select sites in a new tab, saving a tremendous amount of memory and CPU cycles. Session Buddy is another extension that allows you to categorize and save groups of tabs to make it easier to access them later. Kernel Lockdown Feature Coming To Linux 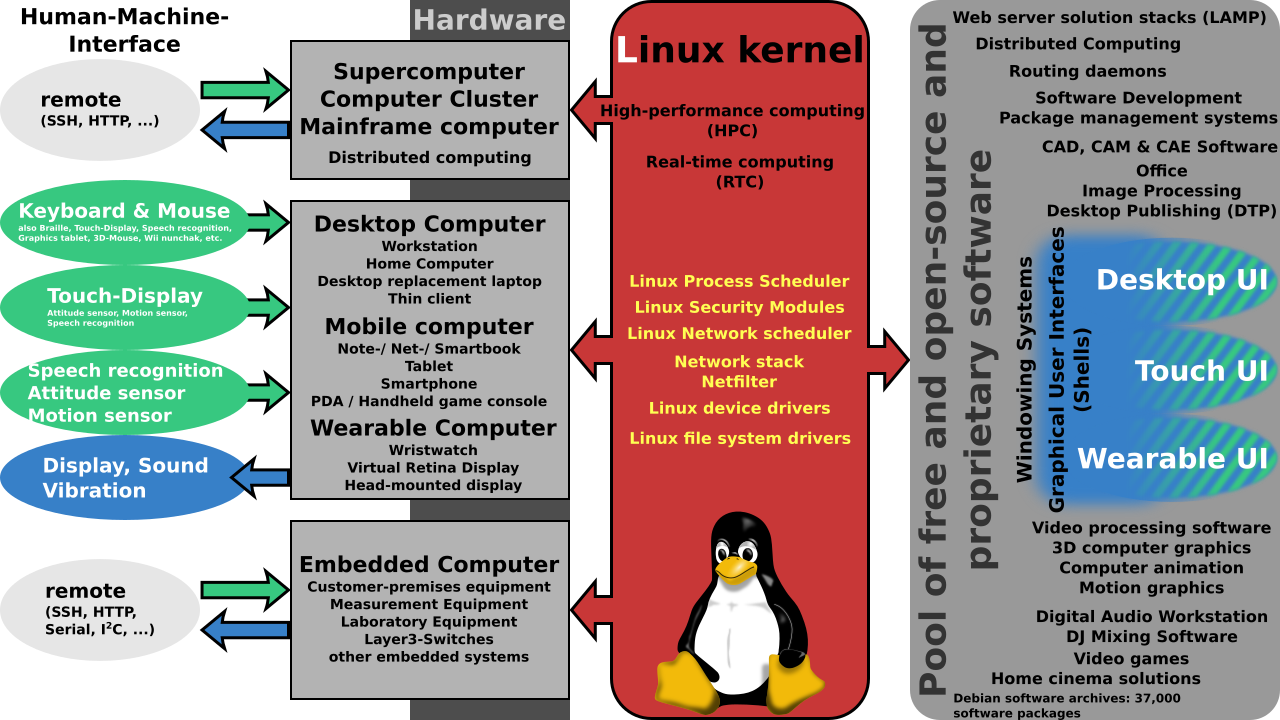 Coming to the Linux Kernel 5.4 branch, the Linux Security Module (LSM) will prevent "high level" access -- in some cases, even root -- from tampering with kernel functionality, according to an article on ZDnet. The feature will (at least initially) be turned off by default, because of the possibility that it might "break" existing systems. Here's an excerpt from the description on the git.kernel.org website: This patchset introduces an optional kernel lockdown feature, intended to strengthen the boundary between UID 0 and the kernel. When enabled, various pieces of kernel functionality are restricted. Applications that rely on low-level access to either hardware or the kernel may cease working as a result - therefore this should not be enabled without appropriate evaluation beforehand. The LSM should strengthen security by widening the division between userland and the kernel. The new module should restrict certain kernel functionality, even for the root user. This should make it harder for compromised root accounts to wreak havoc on the rest of the operating system. The LSM module has two lockdown modes. "If set to integrity, kernel features that allow userland to modify the running kernel are disabled," said Torvalds. "If set to confidentiality, kernel features that allow userland to extract confidential information from the kernel are also disabled." The new lockdown feature got its start in the early 2010s, and was spearheaded by Matthew Garrett, now a Google engineer. The main objections to it came from Linus Torvalds, as evidenced in this 2013 article on ArsTechnica (warning: adult language at link). As a result, some Linux vendors (such as RedHat) created their own security module separate from the kernel, that ran on top of the kernel. A middle ground was reached between the parties in 2018, and work has progressed from there. The move has been lauded by the Linux community and cybersecurity experts alike. Firefox Extension Hides Detection Of Private Browsing Mode  Most browsers today sport a private browsing mode, including Firefox. Users have demanded it, since little to no information from a private browsing session is saved as a permanent record. It helps insure privacy, and that users aren't tracked as easily from site to site to site. Some users use private browsing mode almost exclusively. A few months back, Google Chrome developers attempted to close a loophole that allowed paywall sites and other sites to detect when a user was using private mode browsing. While initially successful, sites wishing to not allow users to use private browsing modes found other workarounds, effectively nullifying the work of the developers. Users utilize private browsing mode for a number of reasons, the least of which is to help insure their privacy. Right or wrong, users also use -- or attempt to use -- private browsing mode to circumvent paywall sites that limit the number of articles a user can read without paying for a subscription. The content providers (typically newspaper and magazine sites) want to limit unfettered access without being paid. Users wanting to circumvent the paywalls liken it to finding a copy of a newspaper in a park refuse bin. They didn't pay for it, but they can still read the content. Plus, no one wants to pay for a subscription to a site that they only occasionally or sporadically read/visit. I first found out about the Firefox Hide Private Mode extension from an article on gHacks. From that gHacks article: The Firefox extension Hide Private Mode disables the workaround (that uses the IndexedDB API). All it takes is to install the browser extension in the Firefox web browser and allow it to run in private windows. Just open about:addons in Firefox, click on the Hide Private Mode extension, and switch the "Run in Private Windows" option from don't allow to allow. Firefox also uses a similar IndexedDB API, just like Chrome. This extension blocks detection of the use of IndexedDB API to signify that the user is using private browsing mode, rendering one of the wor5karound detection strategies useless. What's even better is that the extension is open source, and you can report issues, as well as download/view/contribute to the code, at its GitHub page. HUGE sudo Bug Found!  PCLinuxOS is rather unique among Linux distros in that it does not routinely use sudo to temporarily grant administrative access/rights to ordinary users. For Linux users distro hopping, the lack of the use of sudo is mystifying and puzzling. Virtually every other Linux distro supports the use of sudo. The tool (that is what sudo is, it's a tool) is available for installation from the PCLinuxOS repository, but it typically is not installed by default. Old-Polack wrote a forum post explaining why PCLinuxOS shuns the use of sudo. We even ran that post in The PCLinuxOS Magazine as an article in the May, 2012 issue. When used as intended, sudo is usually a fairly safe tool. But, when used improperly, sudo can be a nightmare for system security. So, when a new security bug was found in sudo (CVE-2019-14287), most PCLinuxOS users were not affected. Present in versions of sudo prior to 1.8.28 (which is also the latest version available in the PCLinuxOS version), setting sudo to execute as user -1 or 4294967295 treated the user as user 0, or the root user. According to an article on The Hacker News: Since the attack works in a specific use case scenario of the sudoers configuration file, it should not affect a large number of users. However, if you use Linux, you are still highly recommended to update sudo package to the latest version as soon as it is available. ? So, if you've installed sudo in PCLinuxOS previously, be sure to run updates on your system to resolve the security issue.
GNOME files defense against patent troll  A month ago, GNOME was hit by a patent troll for developing the Shotwell image management application. It's the first time a free software project has been targeted in this way, but we worry it won't be the last. Rothschild Patent Imaging, LLC offered to let us settle for a high five figure amount, for which they would drop the case and give us a licence to carry on developing Shotwell. This would have been simple to do so; it would have caused less work, cost less money, and provided the Foundation a lot less stress. But it also would be wrong. Agreeing to this would leave this patent live, and allow this to be used as a weapon against countless others. We will stand firm against this baseless attack, not just for GNOME and Shotwell, but for all free and open source software projects. For these reasons, GNOME Foundation Executive Director Neil McGovern instructed our legal counsel at Shearman & Sterling to file three papers with the court in California. First: a motion to dismiss the case outright. We don't believe that this is a valid patent, or that software can or should be able to be patented in this way. We want to make sure that this patent isn't used against anyone else, ever. Second: our answer to the claim. We don't believe that there is a case GNOME needs to answer to. We want to show that the use of Shotwell, and free software in general, isn't affected by this patent. Third: our counterclaim. We want to make sure that this isn't just dropped when Rothschild realizes we're going to fight this. We want to send a message to all software patent trolls out there — we will fight your suit, we will win, and we will have your patent invalidated. To do this, we need your help. Please help support the GNOME Foundation in sending a message that patent trolls should never target free software by making a donation to the GNOME Patent Troll Defense Fund. If you can't, please help spread the word with your friends on social media. |


