| Previous
Page |
PCLinuxOS
Magazine |
PCLinuxOS |
Article List |
Disclaimer |
Next Page |
Short Topix: 200 Most Common Passwords Of 2020 |
|
by Paul Arnote (parnote) 200 Most Common Passwords Of 2020  Despite the "annual warnings" (which are most likely much, much more frequent), users are still using easy-to-hack, easy-to-crack passwords. I know that, as this magazine's Chief Editor for over 11 years, we have run password articles so many times in the past that it's now impossible to count them all. I know this definitely isn't my first password article of 2020, either. Well, NordPass has released its list of the 200 most common passwords, along with their frequency of use, how many users were found using them, the length of time it took to crack the passwords, and how many times it was exposed. Without much surprise, the top "password" used was 123456. It rose to the number one spot, after occupying the number two spot in 2019. Now, you've got to promise me that you won't LAUGH at some of these passwords! Below is a reprint of the top 20 worst passwords of 2020. 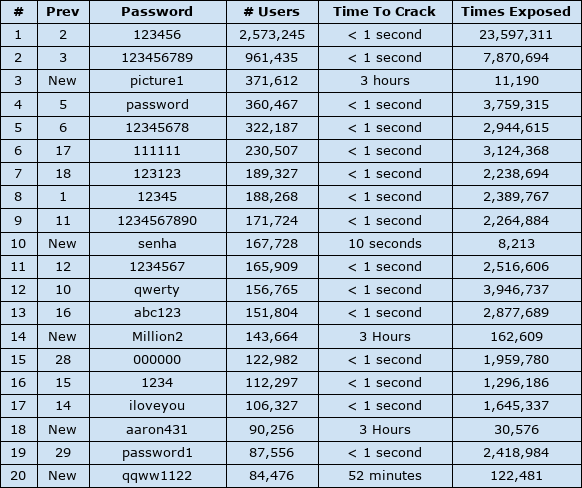 Can you "relate" to any of these "passwords" in this list? If so, don't gloat or be proud. Go out and change them. NOW! Do you also notice that most of these "passwords" were cracked in less than one second? If your chosen "password" has appeared on this list before, then you can count on the hackers to already have it in their special little dictionary of passwords to try first. That special little dictionary of common, previously used, popular "passwords" is used by the software tools the hackers use to gain access to your data in very, very short order. Among the top 20 most common passwords on the list of 200, the longest any of them "held out" before being cracked was three hours. Among the entire list of the 200 most common passwords, the "new" password in the 54th place (jobandtalent) took the longest to crack: three years. You can bet that next year, the time to crack it will be much, much shorter, since it will be added to the "dictionary" used by the hacker's password tools. Let's say you "collect" gold bullion. You store it carefully, stacking it all nice and neat. When you're done counting and stacking your gold, you want to lock it up, to keep others who want to steal your gold from taking it. Would you use a flimsy, mass produced dollar store padlock to secure your gold? Probably not. So why would you do the same thing with your data? Your data is the currency d'jour of the information age. It's YOUR data, and it's YOUR responsibility to protect it. Yes. Others are interested in your data, much like they are interested in your gold. They want to STEAL it! Don't make it easy for them to do so. Go SMS Pro App Exposes Millions Of User Photos, Files  Here's the obligatory, monthly "remove this app from your Android device due to security concerns and stop using this app" article. According to an article on TechCrunch, as well as many other media outlets, the popular Android app Go SMS Pro is exposing photos, videos and files sent privately by millions of its users. The app is listed in the Google Play store as having over 100 million users, so this is a really big deal. Even after being notified by security researchers at Trustwave about the security issue in August, the app maker has done nothing to fix the problem. Efforts by Trustwave, as well as TechCrunch, were unsuccessful at contacting the app maker. So now, three months later, users are being urged to stop using Go SMS Pro, and to remove it from their devices. Specifically, the issue goes something like this. If a Go SMS Pro user sends photos, videos or files to a user who does NOT have the app installed, the files are uploaded to a server, and the non-user of the app was sent a message via SMS text with a link to the files. This way, non-users did not have to install Go SMS Pro just to receive or view the files. At least, that's how it was supposed to work. However, researchers discovered that even when files were shared between users who both had the app installed, files were still uploaded to the servers. What's worse, the server was unsecured, and could be accessed by anyone with the link. Researchers also discovered that the web addresses were sequential, which means that anyone who could figure out the predictable web address could potentially gain access to millions of private files. TechCrunch verified the Trustwave findings, as below: TechCrunch verified the researcher's findings. In viewing just a few dozen links, we found a person's phone number, a screenshot of a bank transfer, an order confirmation including someone's home address, an arrest record, and far more explicit photos than we were expecting, to be quite honest. Hmmm. I guess the number of downloads in the Google Play store are NOT indicative of a trustworthy app, after all. Linux Foundation and NCWIT Release Free Training Course on Diversity in Open Source  The Linux Foundation (November 13, 2020, by Dan Brown) -- Inclusive Open Source Community Orientation (LFC102) is a new training course from The Linux Foundation and National Center for Women & Information Technology (NCWIT) and is designed to provide essential background knowledge and practical skills to create an inclusive culture in the open source community. The course delves into facts about diversity in tech, the importance of diversity for innovation, the basics of unconscious and societal bias, and how to recognize the different ways unconscious bias presents itself in technical environments. The course also provides the knowledge and skills to recognize, appreciate, and include people of differing races, ethnicities, genders, ages, abilities and other identity categories and promote inclusivity and diversity in open source communities. "The research is clear: a variety of cultural factors and implicit biases prevent many people from meaningful participation in technology cultures," said Dr. Catherine Ashcraft, Director of Research, NCWIT. "The practices we suggest in the course are intended to address these multiple biases and make the open source community a more inclusive place where currently underrepresented groups are able to thrive and make meaningful contributions to future technical innovations." While the 2020 Open Source Jobs Report found efforts by employers to increase diversity in open source hiring activities have increased, there is still progress to be made. 11% of those surveyed for the report stated they have been discriminated against or felt unwelcome due to their personal characteristics, an increase from 8% just two years ago. This course is meant as a starting point for everyone in the community -- from technical staff to managers, executives, support teams and more -- to learn more about these issues and how to ensure everyone feels comfortable in the workplace and broader community. "Open source projects are best when they cultivate contributions from a wide range of individuals with different backgrounds from all over the world, so it is prudent for community members to ensure everyone feels welcome," said Chris Aniszczyk, CTO of the Cloud Native Computing Foundation (CNCF). "This course will guide open source projects on how to build inclusive communities, which is why we will be planning to require all CNCF project leadership to complete this training starting next year." LFC102 is available for immediate enrollment at no cost to students. The course complements the existing LFC101 -- Inclusive Speaker Orientation which provides knowledge of how to ensure inclusivity in presentations, messaging and other communications. Enroll today and help build an inclusive open source community! The History Of Ctrl-Alt-Delete  In the computing world, it's commonly and affectionately known as the "three finger salute." But no matter what you call it, I'm betting you never thought much about its origins. Like many users, you were just glad that it was there for your use when you needed it. In an article from Mashable, Virginia Hughes explores the history of how the keystroke combination came to be. And, it's quite a story. In a summarized version, back when PCs were just "born," every time programmers encountered a bug that locked things up, they had to do a hard reboot. There was no other option. And every time you did a hard reboot, early PCs had to perform a RAM check, which took away time from writing code. So, in the Spring of 1981, while working on the Acorn project for IBM, David Bradley created a keyboard shortcut that triggered a system reset, without having to perform the memory check. Never intending for his shortcut to make its way to PC customers, it went on mostly unnoticed ... until Windows and its "blue screen of death" terrorized users. Then, word quickly spread of a quick fix: Ctrl + Alt + Del. Go ahead ... read more about it at the Mashable link above. There is more to the story, and I don't want to steal Ms. Hughes thunder. It is a fascinating story from the times of the origins of the PC. Red Bull Rubik's Cube World Cup 2020  From the Rubik's blog -- The 40th anniversary of the Rubik's Cube becoming a worldwide phenomenon also happens to be the same day as the digital Red Bull Rubik's Cube World Cup FINAL (7 November 2020). Utilising the new digital Rubik's Connected Cube, the final featured some of the best Speedcubers in the world! The new Rubik's Connected Cube enabled the competition to be a virtual tournament in 2020, the first ever digital speedcubing competition. Not only is the new digital Cube a natural progression in the evolution of Rubik's, the launch happened to coincide with a time when people were unable to travel and participate in physical events, in the wake of the COVID-19 pandemic. Here are the results from the 2020 competition:
SPEEDCUBING MIXED
SPEEDCUBING FEMALE
FASTEST HAND
RE-SCRAMBLE Re-watch the 2020 World Cup Final Want to battle the best speedcubers in the world and improve your own solve time? Get your own Rubik's Connected Cube now! Open Source Web Engine Servo to be Hosted at Linux Foundation The popular and lightning-fast web engine built using the Rust programming language will grow the community and expand its platform footprint  KubeCon, November 17, 2020 (by Craig Ross) -- The Linux Foundation, the nonprofit organization enabling mass innovation through open source, today announced it will host the Servo web engine. Servo is an open source, high-performance browser engine designed for both application and embedded use and is written in the Rust programming language, bringing lightning-fast performance and memory safety to browser internals. Industry support for this move is coming from Futurewei, Let's Encrypt, Mozilla, Samsung, and Three.js, among others. "The Linux Foundation's track record for hosting and supporting the world's most ubiquitous open source technologies makes it the natural home for growing the Servo community and increasing its platform support," said Alan Jeffrey, Technical Chair of the Servo project. "There's a lot of development work and opportunities for our Servo Technical Steering Committee to consider, and we know this cross-industry open source collaboration model will enable us to accelerate the highest priorities for web developers." Servo is an open source project that delivers components that can load, run, and display web pages, applications, and immersive WebXR experiences. Developers can integrate the Servo web engine -- including a parallelized CSS engine that speeds page load times and improves stability and a rendering engine called WebRender -- into their own user interfaces, 3D experiences, and other products. Servo currently runs on Linux, macOS, and Windows, and has been ported to devices such as Android phones, Oculus, Magic Leap, and Microsoft's HoloLens. Servo was instrumental in building Mozilla's Gecko browser engine that powered the launch of the Firefox Quantum web browser in 2017, and is still core to Firefox's DNA today. In 2012, Mozilla started the Servo project, a community effort to create a new, open source browser engine that can take advantage of multicore hardware to improve speed, stability, and responsiveness. Today, Servo is more efficient than most web engines because it takes advantage of low-power multi-core CPUs. This is enabled by the open source Rust programming language that focuses on speed, memory safety, and parallelism. Rust and Servo co-evolved, and during their early days, Servo was the only large-scale Rust program other than the Rust compiler itself. Rust's memory safety guarantees mean that Servo presents a smaller attack surface for security vulnerabilities such as buffer overflow attacks. Rust and Servo were both incubated by Mozilla, and the next step for Servo is through the Linux Foundation. "Mozilla is a champion of the open source movement, working to unite passionate communities to build software that keeps the internet open and accessible to all," said Adam Seligman, Chief Operating Officer at Mozilla. "We're pleased to see Servo graduate from Mozilla and move on to the Linux Foundation where we know this technology will continue to thrive and power web-based innovation in the future." "Servo is the most promising, modern, and open web engine for building applications and immersive experiences using web technologies, and that has a lot to do with the Rust programming language," said Mike Dolan, senior vice president, and general manager of projects at the Linux Foundation. "We're excited to support and sustain this important work for decades to come." For more information about the Servo project and to contribute, please visit servo.org. |